Threat to data is real: passwords won’t protect you or your company anymore
by Bija Knowles
The largest database of its kind – containing 1.4 billion unencrypted, stolen credentials from 252 security breaches – on the dark web was made public by security analysts at 4iQ in December 2017. The database is aggregated and searchable, a real treasure-trove for amateur hackers.
“Organizations and individuals who were affected by the numerous data breaches over the past couple of years and have not taken action in terms of changing passwords, canceling debit and credit cards, or requesting a freeze on their credit, are rolling the dice,” writes Vasco's Michael Magrath in this blogpost.
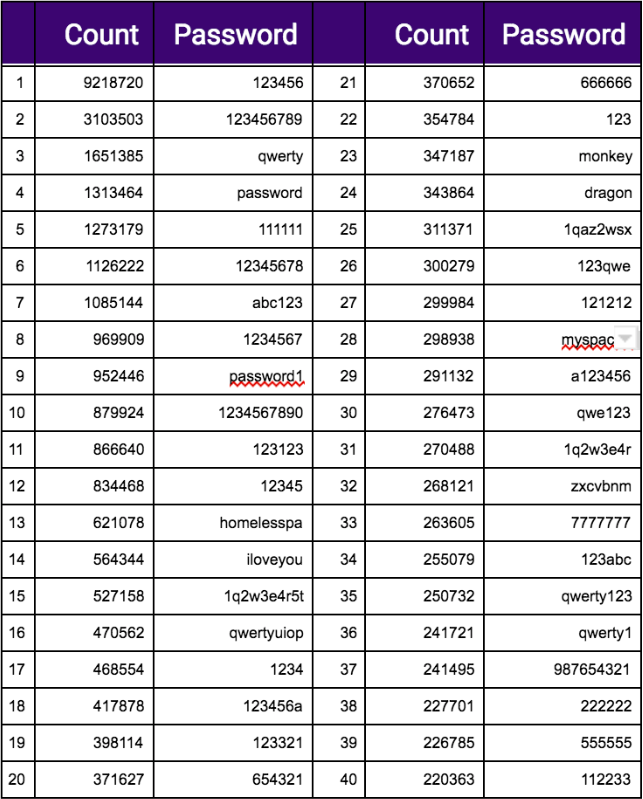
More than 9 million passwords are '123456'
The conclusion is that knowledge-based authentication (KBA) is not enough. Driving this message home, 4iQ analysed the huge database of 1.4 billion unencrypted credentials on the dark web and published the following list of the 40 most common passwords in the database (and the number of times the password appeared). Most of us know by now that '123456' and 'password1' are not the cleverest of ways to outsmart a hacker, but who would have guessed that 'monkey' and 'dragon' would be so popular?
Quantum computing poses risk to ecryption
So it's safe to assume that passwords are not hacker-proof. But there's another threat on the horizon posting a risk to all encryption-based authentication. And according to a newly set-up study group, large-scale quantum computers will be able to compromise the security of many commonly used cryptographic algorithms. The group states: “In particular, quantum computers would completely break many commonly used public-key cryptosystems. These cryptosystems can be compromised in roughly the same amount of time required to generate the public-private key pair: less than a second.”
Quantum computing is currently under development but if (or when) it becomes a commercial reality, does this mean the end of security systems based on encryption?
The group has been set up this week by X9, or the Accredited Standards Committee X9 to use its full name, which is a non-profit organisation accredited by the American National Standards Institute (ANSI) to develop both domestic and international standards for the financial services industry. The purpose of the study group is to review the risk posed to the financial services industry by this new and far more powerful breed of computers, based on quantum computing.
What is quantum computing?
For the uninitiated, quantum computing is based on an entirely different system to traditional computers. The latter use 'bits' (binary digits) to process data and instructions as a sequence of binary 0 or 1 values. There's a limit to the problems that can be solved through binary processing and unsolvable problems are considered 'intractable'. Quantum computing, rather than using the bit system, is based on quantum mechanics and the theory that atoms and subatomic particles can exist in more than one state at the same time. Quantum computing uses quantum digits – qubits – to store and process vast amounts of data, with processing power a million times greater that today's computers. It's thought that they have the potential to solve problems currently considered intractable using classical computers. This article by Bernard Marr in Forbes gives a simple analogy of how quantum computing is different: “Instead of bits, which conventional computers use, a quantum computer uses quantum bits—known as qubits. To illustrate the difference, imagine a sphere. A bit can be at either of the two poles of the sphere, but a qubit can exist at any point on the sphere. So, this means that a computer using qubits can store an enormous amount of information and uses less energy doing so than a classical computer.”
X9 explains: “Quantum computers exploit phenomena of quantum mechanics to solve mathematical problems that are difficult or intractable for conventional computers; as a result, large-scale quantum computers will be able to compromise the security of many commonly used cryptographic algorithms. In particular, quantum computers would completely break many commonly used public-key cryptosystems. These cryptosystems can be compromised in roughly the same amount of time required to generate the public-private key pair: less than a second.”
CTMfile take: In particular, X9 is seeking subject matter experts to participate in the group. It's inviting professionals from financial institutions, product manufacturers, government agencies, university research departments and application developers to be part of the initiative. For more information about participating, those interested are invited to get in touch with ASC X9.
Like this item? Get our Weekly Update newsletter. Subscribe today
