Another weak link in cybercrime prevention? Look to your industrial IT systems
by Bija Knowles
Manufacturing companies are the most susceptible to cyber attacks, according to data released by Kaspersky Lab. It found that, in the first half of 2017, industrial-control systems (ICS) computers within manufacturing companies accounted for roughly a third of all cyber attacks detected on ICS computers protected by Kaspersky Lab products. This data was published in the report: Threat Landscape for Industrial Automation Systems in H1 2017, and relates to computers within the industrial infrastructure of organisations (as opposed to corporate structure). The report shows that the peak of attackers’ activity was registered in March, after which the proportion of computers attacked gradually declined from April to June.
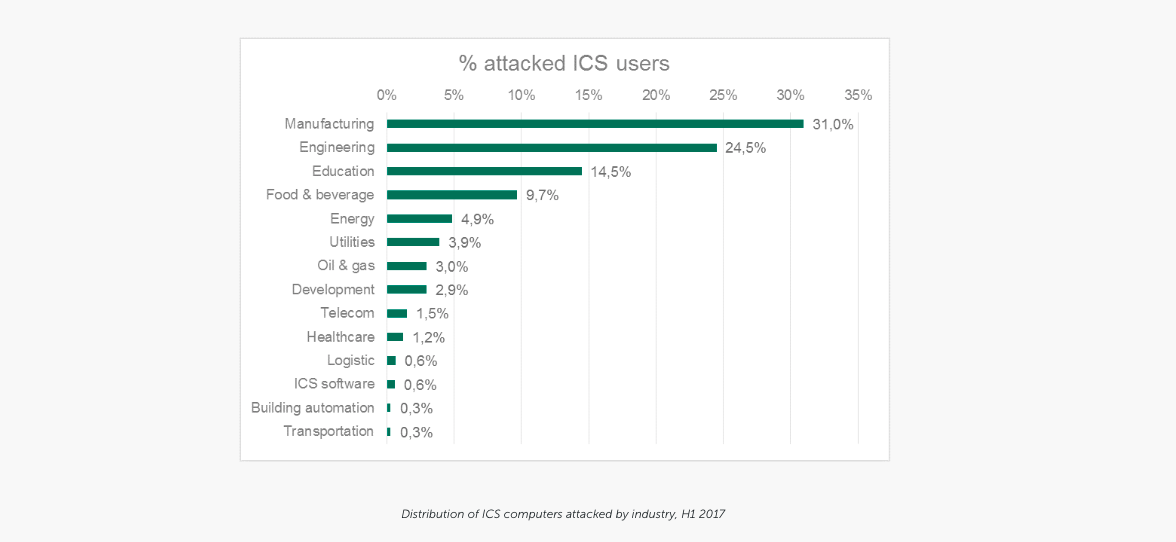
The report said that, during the first six months of the year, the majority of cybercrime attempts on ICS computers were within manufacturing companies, while other industries such as engineering, education and food & beverage were also highly-affected, as shown in the graph below.
Threat of ransomware and phishing on weak systems
There was an increase in detected attacks on industrial computers at Chinese companies but the top three countries suffering the highest rate of cyber attacks were Vietnam, Algeria and Morocco. The greatest threat came from the Internet in the form of attempts to download malware or access known malicious or phishing web resources. Kaspersky Lab said it detected about 18,000 different modifications of malware on industrial automation systems in the first six months of 2017.
The report for the first half of 2017 also found:
- 5 per cent of computers in the industrial infrastructure of organisations were attacked by encryption ransomware at least once;
- ICS computers in 63 countries faced numerous encryption ransomware attacks, the most notorious of which were the WannaCry and ExPetr campaigns;
- the WannaCry epidemic ranked highest among encryption ransomware families, with 13.4 per cent of all computers in industrial infrastructure attacked. The most affected organisations included healthcare institutions and the government sector;
- ExPetr was another notorious encryption ransomware campaign from the first half of the year, with at least 50 per cent of the companies attacked being from manufacturing, and oil & gas industries;
- the Top 10 most widespread encryption Trojan families include other ransomware families, such as Locky and Cerber, operating since 2016 and since that time have earned the highest profit for cybercriminals.
Kaspersky Lab's Evgeny Goncharov said: “In the first half of the year we've seen how weakly protected industrial systems are: pretty much all of the affected industrial computers were infected accidentally and as the result of attacks targeted initially at home users and corporate networks.”
Like this item? Get our Weekly Update newsletter. Subscribe today
